Hiding Secret Files Inside NFTs With Steganography

― George Orwell, 1984
The world of art has always been full of secrets. Maybe by trying to achieve powerful meanings or sometimes by hiding real life secrets, messages, treasures, tributes, techniques or who else knows. Artists love to put their marks on it in order to make it memorable. Take software cracking teams for example, they put their .NFO ascii art files on their releases for increasing respect on the scene. But what happens when the whole world, including the art world enter in a revolutionary state?
Blockchain, mixed reality, qcomputing, NFTs, Ai constructs, a whole new generation where the meaning of art itself have changed and modern technologies have merged the virtual reality with actual reality. We aren’t
too far to experience it everyday of our lives.
If the world change, we as humans must find (cool) ways to adapt to it.
Definitely the world of Non Fungible Tokens took over the scene by converting digital formats like JPG, PNG, GIF, GLB, GLTF, MP3, MP4 into something uncopiable; unique.
Enter Steganography
steg·a·nog·ra·phy | \ ˌste-gə-ˈnä-grə-fē \
Definition of steganography:
1 archaic : CRYPTOGRAPHY
2: the art or practice of concealing a message, image, or file within another message, image, or file.
Steganography is a technique for hiding files inside another files, being an image, a video or anything else. In this case you could send an image of a cute little cat to a friend that contains a secret text file about a corruption scheme in your government. Yes, it’s an old friend of virus developers also.

Many Facebook users discovered the hidden image tags attached to users’ pictures, images can carry a lot of data that’s normally invisible to the human eye. Though, is nothing compared to the sophisticated methods threat actors use to craft images that can deliver malicious code in the wild. Some of them named as Microcin (AKA six little monkeys), NetTraveler, Zberp, Enfal (its new loader called Zero.T), Shamoon, KinS, ZeusVM, Triton (Fibbit) and more.
Digital images are just streams of bytes like any other file, whatmakes them a particularly effective medium for concealing secret text and other data.
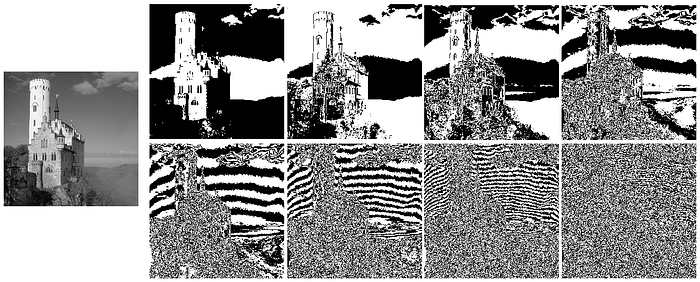
How Steganography Hides Information
To understand how image steganography works, let’s take a look at some basic ways you can hide text in an image file.
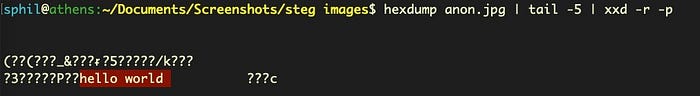
One simple method is simply to append a string to the end of the file. Doing so does not prevent the image from being displayed normally, nor does it change the image’s visual appearance. Here, we simply append “hello world” to the end of the file. The output from hexdump shows us the extra bytes added.

The plain text string can easily be dumped out or read by a program. In this case, we’ll just use the xxd utility to reverse the hexadecimal and print it out in plain text.
echo 68 65 6c 6c 6f 20 77 6f 72 6c 64 0a | xxd -r -p
The same idea can be used to attach a complete file to an image using the RAR archive format. An image viewer only reads the code that relates to displaying the image and ignores any other files contained within the archive. A malicious actor or program, though, can easily extract the appended file.
In this example, the file new.jpg displays a picture when opened in an image viewer application, but when inspected using the WinRaR archiving utility, we can see that the unpacked .jpg file contains a secret 28 byte text file, msg.txt.

Sometimes it can get way bigger than an actual image size, what makes it be recognizable by antiviruses as a malicious archive. But there is always a way around. Always.
A better approach is to get down into the code at a binary level and manipulate the least significant bits (LSB) of individual pixels. Pixels in a color image can be represented by 3 bytes, one each for RGB (Red, Green, Blue). Suppose we have three bytes representing one particular color, in this case orange:
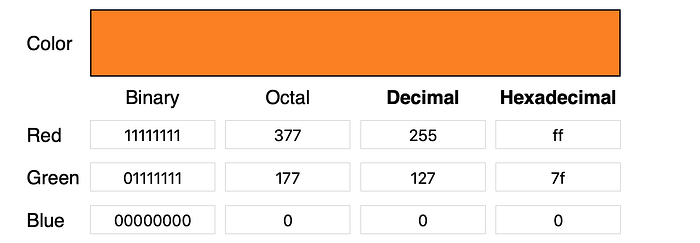
The least significant bits — the last four if we’re reading left-to-right — do not make much of an impact on the color’s visual appearance.
1 1 1 1 1 1 1 1
0 1 1 1 1 1 1 1
00000000
We can change those to anything we like and the pixel will still look pretty much the same. So, let’s take a completely different color, turquoise, say :
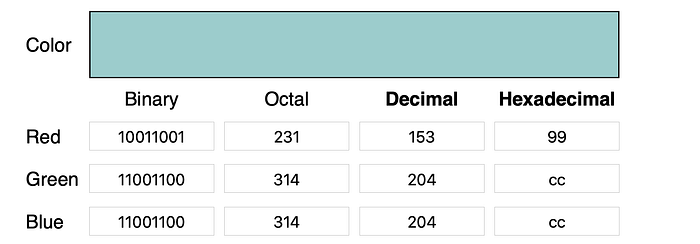
100 1 100 1
1 100 1 100
1 100 1 100
And replace the last 4 bits in the code for orange with the first four bits of the code for turquoise, to produce this composite RGB:
orange turquoise
1 1 1 1 100 1
0 1 1 1 1 100
0000 1 100
There’s no discernible impact on the appearance of the color this generates.
But if we use a program to read and extract these last 4 bits separately, we have effectively hidden the code for turquoise inside the code for orange. Two pixels for the price of one, since there’s no increase in the file size. We can transmit our hidden message without increasing the bandwidth of the original message and without manipulating the file format, so there’s nothing for simple detection methods that rely on file scanning to find.
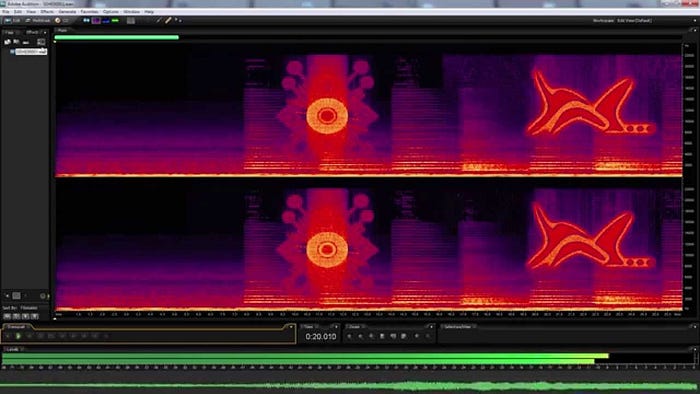
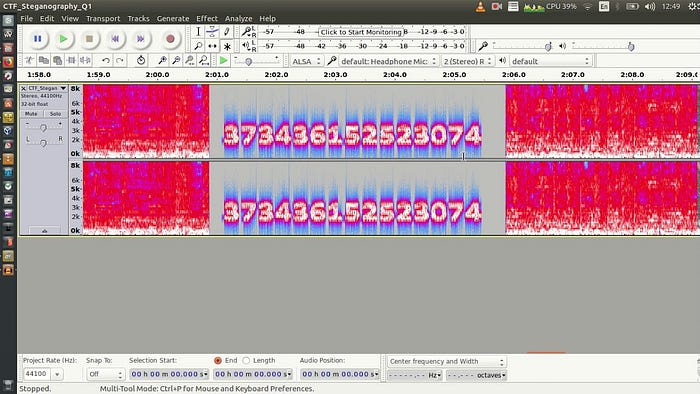
LSB manipulation is only one of a number of steganographic techniques. There are actually a number of other methods by which images and other kinds of files can be manipulated to hide secret code such as Palette Based Technique, Secure Cover Selection, Audio Steganography and many more.
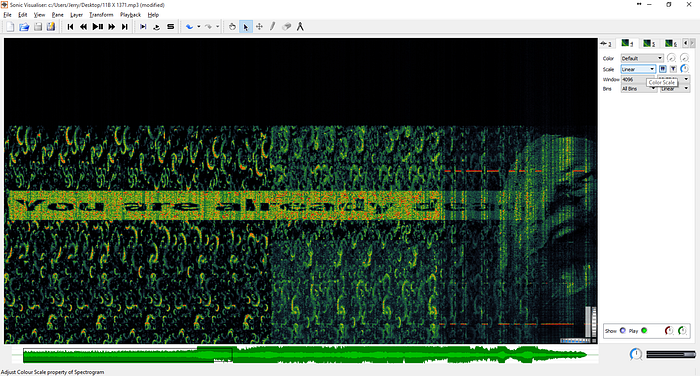

There are many software out there that provide automations for these methods of steganography, so we can cypher our information faster.
Seghide is one great option by the way, and here is a good list of more.
Conclusion
As the art world changes, the techniques changes with it. Hiding information or secrets inside a work is actually another art by itself. In terms of security, there is no perfect system. Every single tech thing around us can be exploited to bring new meanings, reflections and manifestations. Specially wen talking about art.
Now it’s up to us, the artists. What wonders and secrets will be written with steganography in the new world being built around us?
Baby Commando
